Plausible Deniability in Apps: What It Is and Why It Matters
Plausible deniability means hidden data's existence cannot be proven.
Plausible deniability in encryption is the property that allows a user to credibly deny the existence of certain encrypted data. The encrypted storage appears to contain only the data the user chooses to reveal. A forensic examiner, a coercing party, or anyone with physical access to the device cannot prove that additional hidden data exists. This is not a hiding feature. It is a mathematical property of the encryption scheme itself.
This guide explains how plausible deniability works in apps, the difference between genuine cryptographic deniability and cosmetic decoy modes, real-world scenarios where it matters, and how to evaluate deniability claims.
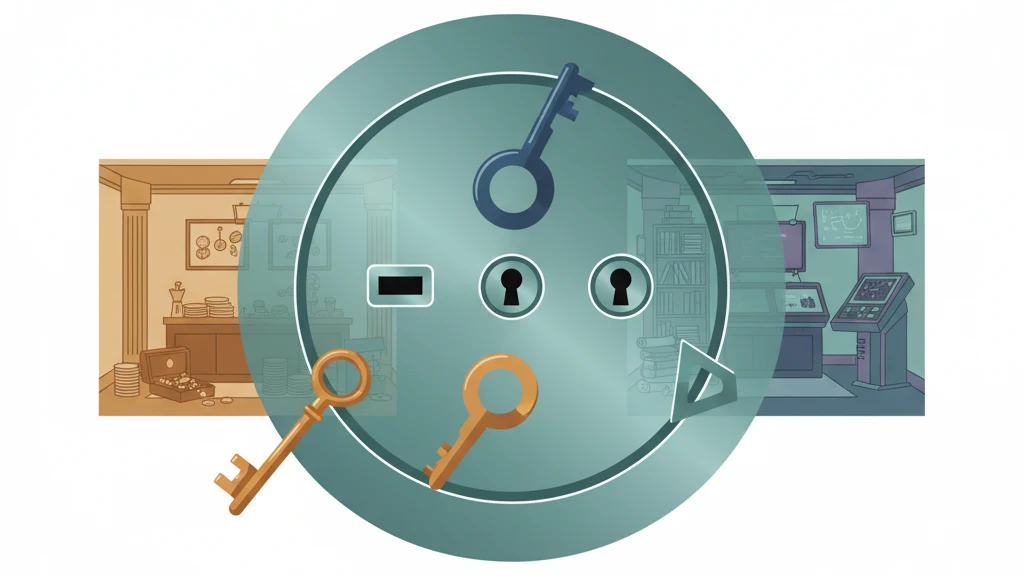
 Image prompt: Flat illustration of a single vault door with three different keyholes. Three different keys float nearby, each in a different color. Behind the door, three different rooms are suggested in ghosted outlines. Muted teal, amber, and blue palette on white background. Style: flat vector, clean design. 16:9, 4K, no text, no watermark.
Image prompt: Flat illustration of a single vault door with three different keyholes. Three different keys float nearby, each in a different color. Behind the door, three different rooms are suggested in ghosted outlines. Muted teal, amber, and blue palette on white background. Style: flat vector, clean design. 16:9, 4K, no text, no watermark.
What Plausible Deniability Means in Encryption
In everyday language, plausible deniability means you can credibly deny something. In cryptography, it means the existence of hidden data cannot be proven, even by an expert with unlimited time and forensic tools.
The concept originated in disk encryption. TrueCrypt (and its successor VeraCrypt) pioneered the hidden volume: an encrypted volume within another encrypted volume. One password reveals the outer volume with innocuous files. A different password reveals the inner hidden volume with sensitive files. A forensic examiner cannot determine whether a hidden volume exists because the unused space in the outer volume is filled with random data that is indistinguishable from encrypted data.
For apps, plausible deniability means that different credentials (passwords, PINs, patterns) open different data sets, and there is no metadata, registry, configuration flag, or structural artifact that reveals the existence of additional data sets.
Genuine Deniability vs. Cosmetic Decoy Modes
This is the critical distinction that most apps get wrong.
Cosmetic Decoy Mode (Not Real Deniability)
Many vault apps offer a "decoy" or "fake PIN" feature. You set a secondary PIN that opens a separate space with different photos. The problem: these apps typically store a boolean flag, a database entry, or a configuration file indicating that a decoy mode exists and is configured.
A forensic examiner who understands the app can find this flag. Finding a configured decoy mode proves that hidden data exists. The deniability is cosmetic -- it works against a casual snoop but fails under forensic examination.
Signs of cosmetic deniability:
- The app has a "decoy mode" toggle in settings
- A configuration file stores whether decoy mode is enabled
- A database table lists vault IDs with type indicators (primary/decoy)
- The app's storage structure changes when decoy mode is turned on
- Uninstalling and reinstalling the app reveals different behavior when decoy mode was configured
Genuine Cryptographic Deniability
Genuine deniability is an architectural property, not a feature toggle. The encrypted storage must be designed so that:
Every credential opens a valid data set. There is no "wrong" password error for credentials that open hidden vaults. Any valid pattern/password combination produces a key that decrypts something.
No vault registry exists. The app cannot enumerate how many vaults exist. There is no count, no index, no list of vault IDs. A forensic examiner examining the app's storage finds an undifferentiated pool of encrypted data.
No configuration flags reveal hidden vaults. There is no boolean, no database entry, no preference file that indicates whether additional vaults exist.
Storage is padded. The total storage consumed does not change based on the number of vaults or files. Without padding, an examiner could estimate the number of vaults from the total encrypted data size versus the visible content.
Encrypted data is indistinguishable from random noise. There are no file boundaries, no headers, no structural markers that reveal where one vault's data ends and another begins.
| Property | Cosmetic Decoy | Genuine Deniability |
|---|---|---|
| Separate data per credential | Yes | Yes |
| No vault registry | No (database tracks vaults) | Yes |
| No configuration flags | No (decoy toggle stored) | Yes |
| Storage padding | Rarely | Yes |
| Survives forensic examination | No | Yes |
| Architectural vs. feature | Feature toggle | Architectural property |
Real-World Scenarios Where This Matters
Plausible deniability is not a theoretical concern. It addresses documented, recurring real-world situations.
Border Crossings
In the United States, Customs and Border Protection can legally compel device access at the border. Courts have ruled that border agents can demand passwords for device inspection. In this scenario, a user with genuine plausible deniability can provide a pattern/password that opens a vault containing innocuous content. The examiner cannot prove that other vaults exist.
Domestic Abuse and Coercive Relationships
Someone in an abusive relationship may need to store evidence (photos of injuries, threatening messages, legal documents) on a device that the abuser monitors. If the abuser demands to see the vault, the user can open a vault with non-sensitive content. Without genuine deniability, a "decoy mode" flag in the app's configuration would reveal the existence of hidden content.
Device Theft
A thief with technical skills might attempt to extract data from a stolen phone. With genuine deniability, the encrypted data pool reveals nothing about the number of vaults, their contents, or their purpose.
Legal and Journalistic Protection
Journalists protecting sources, lawyers protecting client files, and activists in authoritarian regimes face scenarios where device contents can be compelled. Genuine deniability provides a credible defense against data seizure.
How Vaultaire Implements Plausible Deniability
Vaultaire achieves genuine cryptographic plausible deniability through architectural design:
Every pattern opens a different vault. The 5x5 grid produces a key via PBKDF2. A different pattern produces a different key. There is no master key, no vault list, and no way for the app to enumerate existing vaults. Drawing a pattern that has no associated vault simply opens an empty vault space -- there is no "incorrect pattern" error.
No vault registry. The app has no database listing vaults, vault names, or vault counts. All encrypted data exists in a single undifferentiated storage pool. A forensic examiner with unlimited access to the device file system finds encrypted blocks with no structural markers indicating vault boundaries.
Storage padding. The total storage size remains constant regardless of vault count or file count, defeating disk-usage analysis.
No configuration flags. There is no settings file, no preference entry, and no database record that reveals how many vaults exist or whether any specific pattern has been used.
Duress mode. Users can designate one vault as a duress vault. Drawing that pattern opens the vault normally while simultaneously and silently destroying the cryptographic salts for all other vaults. The destruction is irreversible, leaves no forensic trace, and takes under one second.
How to Evaluate Deniability Claims
When an app claims plausible deniability, ask:
- Is there a "decoy mode" toggle? If yes, it is cosmetic. A forensic examiner can find the toggle.
- Does the app have a vault list or database? If yes, vault existence is provable.
- Is there a "wrong password" error? If yes, the app can distinguish between valid and invalid credentials, which means it stores something that validates credentials.
- Does storage consumption change with vault count? If yes, disk analysis can estimate vault count.
- Can the app enumerate vaults? If the app can show you a list of your vaults, that list exists on the device and is discoverable.
Frequently Asked Questions
Is plausible deniability legal?
Using encryption with plausible deniability is legal in most democracies. There is no law against having encrypted data on your device whose existence cannot be proven. In some jurisdictions (UK under RIPA, Australia under the Assistance and Access Act), authorities can compel disclosure of encryption keys. The legal question is whether compelling disclosure of a key to data whose existence cannot be proven is enforceable. This remains a developing area of law.
Can forensic tools detect plausible deniability?
Professional forensic tools (Cellebrite, GrayKey, Magnet AXIOM) can detect that Vaultaire is installed and that encrypted data exists. They cannot determine how many vaults exist, what they contain, or whether additional vaults exist beyond any that are revealed. The encrypted data is indistinguishable from random noise. This is verified by design, not claimed by policy.
Does plausible deniability work against a determined nation-state?
Against cryptanalysis (breaking the encryption): yes. AES-256 is not breakable by any known nation-state capability. Against coercion (forcing you to reveal patterns): plausible deniability means you can reveal one vault while credibly denying others exist. Against device exploitation (using a zero-day to extract data from a running device): if the device is unlocked and the vault is open, the decrypted data is in memory and theoretically accessible. Plausible deniability protects data at rest, not data in active use.
What is the difference between plausible deniability and hidden vaults?
Hidden vaults are vaults that are not visible in the app's interface. Plausible deniability is the property that the existence of hidden vaults cannot be proven. An app can have hidden vaults without plausible deniability (if a vault registry or configuration flag reveals them). Vaultaire provides both: vaults are hidden by default, and their existence is unprovable by design.
Can I use plausible deniability with cloud backups?
In Vaultaire, encrypted iCloud backups contain the entire encrypted storage pool. The backup is a single encrypted blob. It preserves plausible deniability because the backup itself contains no vault-level structure -- it is the same undifferentiated encrypted pool as on-device storage.
Bottom Line
Plausible deniability in encryption means the existence of hidden data cannot be proven, even under forensic examination. Most apps that claim this feature offer cosmetic decoy modes with discoverable configuration flags. Genuine deniability requires no vault registry, no configuration flags, storage padding, and architecturally indistinguishable encrypted data.
Vaultaire implements genuine plausible deniability as an architectural property: every pattern opens a different vault, there is no vault list, storage is padded, and no other encrypted vault app does this.
Last updated: March 2026